A forgotten demo dashboard reveals how China’s security apparatus imagines total data control.
by Tan Liwei

Every so often, a small investigative outlet uncovers something that larger media often overlooks. NetAskari, a cybersecurity research publication specializing in Chinese issues, has done just that. Its research is being debated by Chinese netizens as well, despite censorship. By examining abandoned dashboards left open on the internet, it has pieced together a telling picture of how China’s public security system thinks, plans, and dreams. While the dashboards are mock-ups—student projects, prototypes, and half-finished demos—their content provides a rare glimpse into the mindset behind China’s mass-surveillance goals.
To grasp why this matters, one must first understand the unique ecosystem of “big data dashboards” in China. In recent years, students, junior developers, and contractors have created countless visual interfaces for school assignments, competitions, or pitches. Many of these dashboards are quickly abandoned, left online without passwords. Most pose no threat, but some, as NetAskari shows, act as prototypes for tools that reflect the logic of China’s real surveillance programs.
The central dashboard in this investigation is labeled a “Provincial-level holographic archive system.” The name alone suggests big ambitions: a single interface to track, classify, and analyze individuals across an entire province. The design is basic, the data fake, but the categories are disturbingly real. Individuals are labeled as “Key Personnel,” “Under Surveillance,” “Drug-Related,” or “High-Risk.” Their profiles include ID numbers, phone metadata, GPS traces, financial habits, hospital visits, travel patterns, and even hashes of facial scans and fingerprints. The system envisions a world where every citizen’s relationships, movements, and activities can be mapped and scored.
None of this is science fiction. China’s Ministry of Public Security has spent years developing the infrastructure for such systems: the Xueliang (“Sharp Eyes”) project, expanding facial-recognition networks, integrating telecom data, and creating “holistic relationship models” that connect individuals through co-travel, co-residence, social media, and shared contacts. NetAskari’s discovery does not confirm that this specific dashboard is in use. Still, it illustrates what developers believe the police want—and what the police themselves have detailed in patents, tenders, and internal documents.
The mock-up even has a “risk assessment” tab that provides recommendations for operators, such as deploying early-warning systems at train stations or flagging a person’s contacts for further investigation. It is an imagined omniscience, but one based on real policy goals. Chinese policing practices, under the slogan “smart policing,” explicitly call for integrating multiple data sources to create dynamic, predictive models of “key personnel.” The dashboard visualizes that goal.
NetAskari also points out the peculiarity that this demo was hosted on a server in the United States. Whether it was made by a Chinese student abroad or by a developer testing an idea far from home, the location highlights the accidental transparency of China’s digital ecosystem. These carelessly exposed prototypes provide some of the clearest insights into the architecture of control.
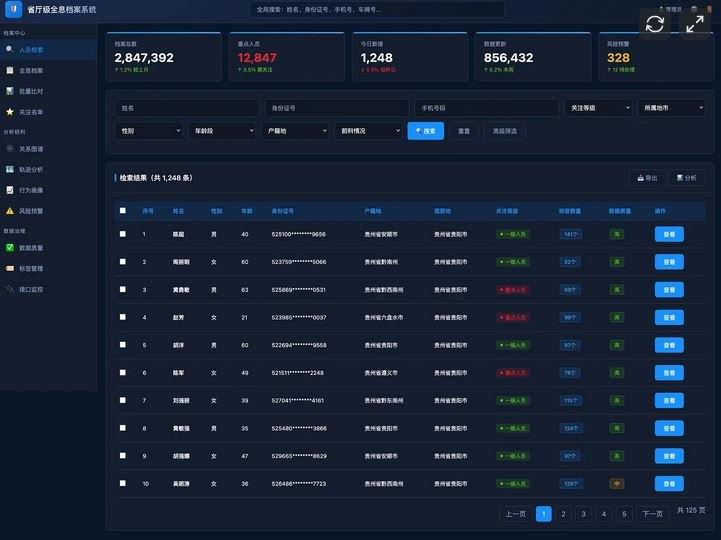
The importance of this investigation lies not in its technical details but in what they reveal about the direction of Chinese governance. China’s security system is shifting to a model where surveillance is proactive rather than reactive, and comprehensive rather than targeted. Even if the technology is flawed, the intention is clear: to create systems capable of tracking entire populations, identifying “abnormal” behavior, and mapping social networks with forensic accuracy.
For readers less familiar with coding, dashboards, or data structures, NetAskari’s work offers something valuable: a translation of technical artifacts into political meaning. It shows how a simple student-level demo can reflect the mindset of a state that aims for total visibility. It also reminds us that mass surveillance is built not just through large national projects but through thousands of small, incremental tools—some polished, some rough around the edges—all pointing in the same direction.
In the end, the unused dashboard is less significant than the mindset it uncovers. It sketches a future where every citizen is a data point, every relationship a potential risk factor, and every movement a line in a police-controlled graph. NetAskari has demonstrated that even the discarded prototypes of China’s digital bureaucracy deserve attention. They are early drafts of a system already reshaping the boundaries of privacy, autonomy, and state power.

Uses a pseudonym for security reasons.